Every Azure landing zone failure I’ve seen starts the same way: someone treated it as a deployment task rather than a foundation. The zone goes live, the team moves on, and six to eighteen months later, the same organization is paying to redesign infrastructure that was never built to evolve. If you’re responsible for Azure at scale, this post covers the specific patterns that cause that outcome and how to avoid them.
Table of Contents
- Defining Azure Landing Zones and Their Purpose
- Static Setup Mindset: A Costly Anti-Pattern
- Critical Gaps in Hub-Spoke and Governance
- Preventing Failure Through Continuous Evolution
Key Takeaways
| Point | Details |
|---|---|
| Living Framework | An Azure landing zone must be treated as a dynamic system requiring ongoing updates and reviews to remain effective against evolving threats and compliance requirements. |
| Clear Responsibilities | Clearly delineate between platform and application teams to prevent chaos and ensure security and compliance across Azure resources. |
| Governance Importance | Establish a governance structure early to avoid compliance issues and mismanaged resources within a hub-and-spoke architecture. |
| Quarterly Reviews | Implement a quarterly governance review process to assess and adjust policies, network architecture, and compliance status for continual improvement. |
Defining Azure Landing Zones and Their Purpose
An Azure landing zone isn’t a product you deploy once and forget. It’s a standardized foundation that prepares your entire Azure environment for growth, security, and operational control from day one.
I tell clients this upfront: if you’re treating a landing zone as a checkbox item, something to tick off before moving workloads, you’re already behind. The organizations I work with that succeed understand this is a living framework, not a one-time setup.
At its core, a landing zone provides a consistent way to structure subscriptions, governance policies, and networking architecture. It establishes boundaries between teams, enforces security controls before they’re needed, and prevents the sprawl that derails most Azure migrations.
Here’s what actually happens in practice:
- Security baseline: Built-in policies prevent unauthorized resource creation before violations occur
- Network isolation: Hub-and-spoke topology (or Virtual WAN patterns) enforce traffic control at scale
- Billing and cost controls: Subscription organization and tagging standards from the start
- Compliance readiness: Audit logs, role-based access, and policy assignments live in the foundation
- Operational consistency: Teams follow the same naming conventions, deployment patterns, and runbooks
The real value isn’t what you deploy in month one; it’s what you prevent from breaking in months 6 through 36.
Too many organizations I consult with built their landing zones around immediate use cases, then discovered they’d hardcoded assumptions about team size, workload types, or compliance requirements. Eighteen months later, they’re fighting architectural debt they could have avoided.
A proper landing zone separates platform responsibilities from application responsibilities. Platform engineers own the hub network, policies, identity infrastructure, and shared services. Application teams own their subscriptions within those guardrails. This separation prevents the chaos of 47 different teams managing their own network security rules.
Your landing zone should answer these questions before you deploy anything:
- Who can create resources, and what types?
- How do networks communicate across teams?
- Where do logs go, and who can access them?
- How are costs allocated and monitored?
- What happens when a team violates a policy?
Pro tip: Start with a single landing zone for pilot workloads, document every assumption you make about team structure and compliance needs, and plan for evolution. Your landing zone in year two will look different than year one, and that’s healthy if it’s intentional.
Here’s a summary of platform vs. application team responsibilities in an Azure landing zone:
| Responsibility Area | Platform Team | Application Team |
|---|---|---|
| Network Design | Build hub topology | Use provided network |
| Policy Management | Enforce global policies | Follow defined guardrails |
| Cost Allocation | Define tagging strategy | Tag resources per guidelines |
| Compliance Auditing | Monitor, update standards | Maintain workload compliance |
| Resource Deployment | Provision shared services | Deploy app-specific resources |
Static Setup Mindset: A Costly Anti-Pattern
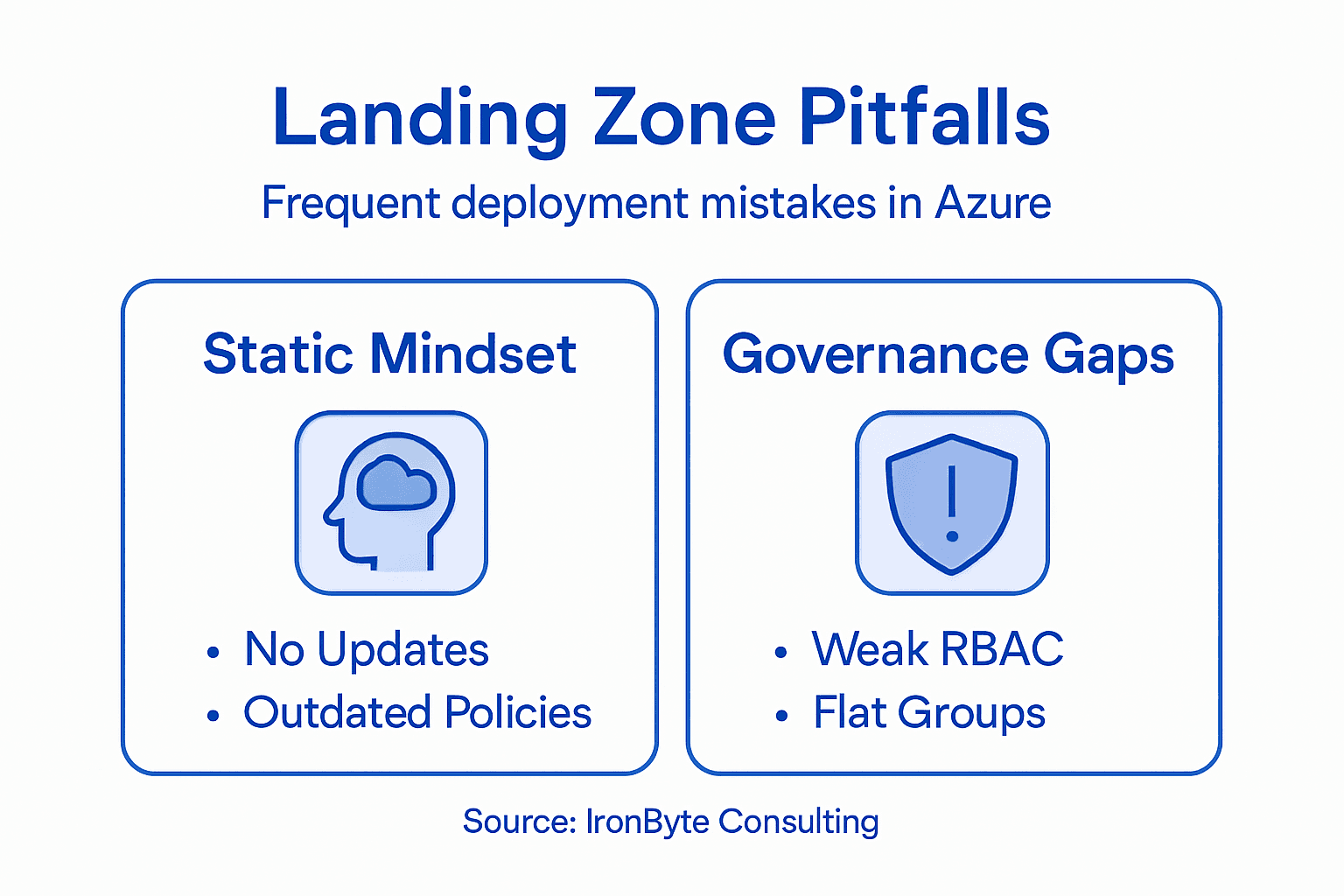
Here’s what I see repeatedly: organizations deploy a landing zone, declare victory, and don’t touch it for two years. By then, the threat landscape has shifted, compliance requirements have changed, and their entire setup is quietly failing audits.
This is the static setup mindset, and it’s one of the most expensive mistakes in Azure deployments.
When you treat a landing zone as a “set and forget” infrastructure piece, you’re making an implicit assumption that threats, regulations, and business needs stay constant. They don’t. Security vulnerabilities emerge monthly. Compliance frameworks evolve. Your organization’s team structure changes. Yet the landing zone remains frozen.
I worked with a financial services firm that built their landing zone around 2022 compliance requirements. They deployed Azure Policy to enforce those standards, configured their hub-and-spoke network topology, and handed it to operations. Eighteen months later, a new regulatory requirement arrived, but their policies were so rigid they couldn’t adapt without complete redesign. The cost of reworking the foundation exceeded what a flexible approach would have cost initially.
Zero Trust principles require continuous adaptation, not a one-time configuration. Your landing zone needs to evolve as threats change.
Here’s what static landing zones typically miss:
- Stale Azure Policies: Rules written for last year’s threats don’t prevent this year’s attacks
- Rigid network topologies: Hub-spoke patterns that seemed perfect in month one often need adjustment
- Unchanged RBAC: Role assignments accumulate without cleanup, violating least-privilege over time
- No threat intelligence integration: Manual policies don’t respond to emerging attack vectors
- Compliance drift: Audits reveal violations because standards changed but the landing zone didn’t
A landing zone deployed in 2023 with 2023 assumptions will actively hinder you by 2025.
The antidote is treating your landing zone as infrastructure that requires ongoing review. Schedule quarterly reviews of your Azure Policies, assess whether your network design still fits your topology, validate RBAC assignments, and check whether compliance requirements have shifted.
Platform engineering teams I work with now build landing zones with intentional versioning. They document assumptions explicitly, set calendar reminders for policy reviews, and plan incremental updates rather than avoiding the foundation altogether.
Pro tip: Establish a quarterly “landing zone health check” where you review policy effectiveness, audit logs for policy violations, and validate whether your current network and identity design still matches your organization’s real structure, not the org chart from deployment day.
To highlight the differences between dynamic and static Azure landing zone approaches, see the table below:
| Approach | Adaptability | Risk | Maintenance Effort |
|---|---|---|---|
| Static Setup | Low; Rare updates | High; Falls out of compliance | Minimal but causes technical debt |
| Continuous Evolution | High; Regular reviews | Lower; Remains audit-ready | Intentional, scheduled improvements |
Critical Gaps in Hub-Spoke and Governance
Hub-and-spoke topology sounds elegant on a whiteboard. One central hub handles all traffic, spokes connect to it, and everything flows through controlled pathways. But I’ve watched this pattern create governance nightmares that take months to untangle.
The problem isn’t the topology itself. It’s what organizations leave out when they build it.
Most teams focus on the network piece, drawing diagrams of ExpressRoute connections and Azure Firewalls. They miss the governance layer entirely. Without explicit management group hierarchy and Azure Policy enforcement, a hub-and-spoke network becomes a shell that looks secure but isn’t.
I consulted with a healthcare organization that deployed hub-and-spoke correctly from a networking perspective. Traffic flowed through the hub. Firewall rules worked. But they’d built no governance boundaries between spoke subscriptions. Teams in different spokes could peer networks without approval. Resource groups lacked consistent naming. Policies weren’t enforced at the management group level. One team created a storage account with public access, violating compliance requirements. Nobody caught it because policies weren’t there to prevent it.
Key design areas like identity management and resource organization must be architected alongside network topology, not after.
Here’s what governance gaps typically look like:
- No management group structure: All subscriptions sit at the same level; policies can’t target specific business units
- Weak RBAC model: Identity access tied to resource names rather than logical ownership
- Missing policy scope: Policies exist but aren’t linked to management groups consistently
- Undefined approval workflows: Teams don’t know who owns network peering decisions
- Inconsistent tagging: Cost allocation and resource tracking fail because tags are optional
- No audit trail for changes: Who deployed that firewall rule? When? Why? Nobody knows.
A perfectly designed hub-and-spoke network with zero governance is just plumbing without guardrails.
I now work with clients to build governance first, then layer the network topology on top. Start with a management group hierarchy that reflects your organization’s actual structure, not the ideal org chart, but the real one. Assign policies at the root level and override selectively. Define RBAC using job functions rather than team names. Document approval workflows before the first spoke connects.
The technical setup takes two weeks. The governance setup takes two months because it requires decisions, not just configuration.
Pro tip: Before deploying a single ExpressRoute connection, map your management group hierarchy on paper and assign at least five core Azure Policies at the root level, then test them on a non-production subscription to catch conflicts before they cascade across your spokes.
Preventing Failure Through Continuous Evolution
Organizations that succeed with Azure don’t build a landing zone and move on. They treat it as a living system that improves quarterly, adapts to new threats, and evolves with business priorities.
This is the difference between a landing zone that supports growth and one that constrains it.
I worked with a manufacturing company that established its baseline landing zone, organized subscriptions, put basic policies in place, and deployed a hub-and-spoke network. Then they stopped. Six months later, a new business unit was acquired. Their landing zone couldn’t accommodate the acquisition’s compliance requirements without complete restructuring. What should have been a simple onboarding became a three-month remediation project.
The companies I work with that avoid this mess establish a management baseline first, then progressively enhance it. This baseline covers inventory, operational compliance, and recovery capabilities, creating a foundation that can scale without breaking.
The exact sequence varies by organization, but the principle holds: start with core policies, basic RBAC, and a hub-and-spoke network in the first phase. Add backup, disaster recovery, and monitoring next. Then, cost optimization and naming refinement. Security scanning and threat-response policies come later, once you have stable visibility into what your environment actually looks like under real load. Each phase builds on the last without disrupting what’s running. The mistake is trying to do it all at once, or, worse, doing none of it after month one.
A landing zone is never complete. It’s only complete enough for this quarter.
The key is intentional prioritization. You can’t tackle everything simultaneously. Pick three improvements per quarter aligned with actual business needs, not theoretical perfection. One client prioritized cost controls first because their finance team was bleeding budget visibility. Another prioritized security scanning because they faced an upcoming audit.
Most teams fail at this because they lack a governance review cadence. Quarterly reviews aren’t optional; they’re infrastructure maintenance. During these reviews, assess policy effectiveness, validate that your naming standards are working, check for resources that are out of compliance, and identify the next 3 improvements.
Document what you change and why. Future you won’t remember why that policy exists unless you wrote it down.
Pro tip: Establish a quarterly governance council meeting (one hour, same day every quarter) where platform engineers, security, and business stakeholders review landing zone health, audit policy violations, and agree on three specific improvements for the next quarter, then assign ownership and track completion.
Master Azure Landing Zones with IronByte Consulting & Training
Struggling with hidden pitfalls that sabotage your Azure landing zone deployment?
The article highlights critical challenges, including static setup mindsets, governance gaps, and inflexible hub-and-spoke architectures, which lead to costly rework and compliance risks. If you want to avoid architectural debt, prevent security blind spots, and ensure your cloud foundation evolves dynamically, you need expert guidance rooted in deep Azure experience and proven governance frameworks.
At IronByte Consulting & Training, we specialize in delivering senior-level Azure expertise that empowers enterprises to build robust, adaptable landing zones from day one. Our strategic architecture design and governance services ensure your landing zone is a living system that evolves with your business needs and security landscape. Learn how to implement continuous evolution, strong policy enforcement, and operational consistency with us. Don’t wait until compliance audits or new threats force expensive fixes. Take the next step toward scalable cloud success by visiting our main site and discovering how our custom consultancy transforms your Azure foundation today.
Frequently Asked Questions
What is an Azure landing zone?
An Azure landing zone is a standardized foundation designed to prepare your Azure environment for growth, security, and operational control right from the start. It involves structuring subscriptions, governance policies, and networking architecture to enforce security and prevent resource sprawl.
Why is a dynamic approach important for Azure landing zones?
A dynamic approach ensures that your landing zone evolves continuously to address changing security threats, compliance requirements, and organizational structures. A static setup can lead to outdated policies and risk non-compliance, causing potential failures during audits.
How do governance gaps impact Azure landing zones?
Governance gaps, such as missing management group structures and weak role-based access control (RBAC), can lead to security violations and compliance issues. Without proper governance in place, teams might have unauthorized access to resources, compromising overall security.
What are the key responsibilities of platform and application teams in Azure landing zones?
Platform teams are responsible for building the network architecture, enforcing global policies, and managing cost allocation. In contrast, application teams manage their specific subscriptions within those policies, ensuring compliance and deploying application-specific resources.
Recommended
- Azure Architecture & Landing Zones – IronByte Consulting and Training
- Advanced Architecture & Enterprise Patterns – IronByte Consulting and Training
- Cloud Readiness & Roadmap – IronByte Consulting and Training
Both options go directly to me. No sales funnel, no account managers.